In a context where organizations are increasingly dependent on technology, risk management has evolved from an isolated technical function into a strategic pillar of organizational resilience. Between regulatory pressure and the growing sophistication of digital threats, managing risks in a structured way is essential to ensure operational continuity.
Overview
With accelerated digitalization, information systems have become more complex and interdependent. This reality exposes companies to risks that are harder to predict and control, reinforcing the need for a proactive approach to risk management.
Frameworks such as ISO/IEC 27001 and the NIST Cybersecurity Framework (CSF) serve as guides to identify, assess, mitigate and monitor risks from the early stages of system development and operations.

What Are The Most Common Risks In Software And Integration Projects?
- Technical risks: integration errors, unstable APIs, untested dependencies, failures in environments.
- Team risks: knowledge loss, resource changes, poor communication.
- Operational risks: poorly planned deployments, incomplete testing, lack of rollback procedures.
- External risks: third-party service outages, licensing issues, vulnerable open-source components.
How To Approach Risk Management In IT
A practical approach would be to adopt frameworks like the NIST CSF (National Institute of Standards and Technology – Cybersecurity Framework), one of the most widely used tools to structure risk management in technological environments.
Originally created for critical infrastructures, the NIST CSF is now broadly adopted in software companies, cloud services, telecommunications and system integration environments due to its modularity, flexibility and applicability to any type of organization.
The framework is divided into five core functions:
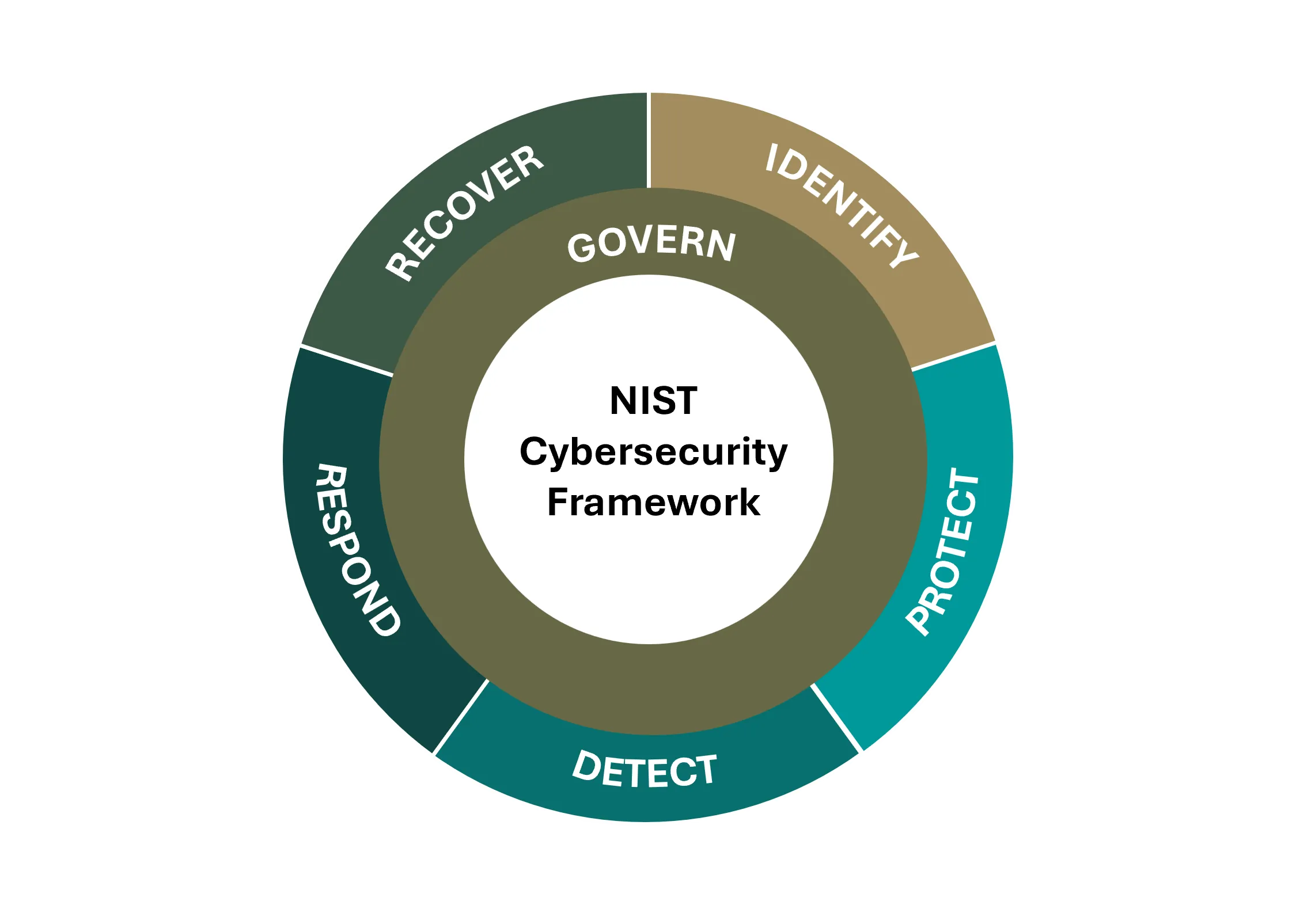
- Identify – Map systems, processes, assets, and associated risks
- Protect – Implement technical and organizational controls (e.g., access control, encryption, training)
- Detect – Monitor the environment to detect anomalies or incidents
- Respond – Define quick response plans for failures and events
- Recover – Ensure recovery and continuity after an outage or attack
Complementary Tools And Best Practices
- ISO/IEC 27001: focuses on information security and supplier control
- OWASP SAMM / ASVS: practical guidance to apply security throughout the Software Development Life Cycle (SDLC)
- Automated security testing: SAST, DAST, fuzzing, and vulnerability scans
Final Thoughts

Risk management in IT projects is no longer an “extra” reserved for security teams or audit checkpoints. It’s a transversal necessity that should be part of the planning, development, integration and operation of any technological system or service.
With the growing adoption of agile methodologies, continuous integration pipelines (CI/CD), distributed architectures and intensive use of external components, the number of potential failure points has increased — and so have the risks.
Fortunately, many frameworks and best practices already provide solid structures that help teams integrate risk management naturally into their daily workflows. From standards like ISO/IEC 27001, with a systematic view of information security, to models like NIST CSF, OWASP SAMM, or even more pragmatic approaches tailored to the DevOps and DevSecOps world — they all share the same principle: anticipate, mitigate and control risks before they become incidents.
Investing in risk management is an investment in business stability, user trust and the technological maturity of the organization. And the sooner you start, the more natural and effective the practices become.
